Hear our team discuss why often, many organizations don’t do a great job of completing a deliberate after-action review process or developing effective after-action reports (AARs) after incidents, from small-scale events to significant threats, such as the current COVID-19 pandemic. The webinar covers topics such as how to get started on an AAR process by identifying the needed resources and getting those resources to conduct the necessary analysis in order to draft an After-Action Report and Improvement Plan. Andy also shares some thoughts on the importance of preparedness and imagination when working towards personal, organizational and national resilience.
To complement our monthly Gate 15 Podcast, we’re happy to introduce our new Security Panel Discussion, now available to listen to wherever you hear your favorite podcasts. This will be the first in a new podcast offering from The Gate 15 Company on The Gate 15 Pod Channel.
In this episode, we welcome security experts Bridget Johnson and Travis Moran, as well as Gate 15 Managing Director Andy Jabbour, to talk about terrorism, extremism, drones and surveillance measures in the COVID world.
Register for our upcoming webinar discussion, “Getting Started Now: Pandemic Preparedness After-Action Reports (AAR)”. Day: 16 April 2020 Time: 1:30pm…
I get asked a lot of questions about Gate 15, like, “what does Gate 15 mean?” (see here – Gate 15: What’s in a Name?
– for that answer). I also get a lot of questions about two other areas. One of those is about the SUN, our free daily online paper. The other is about our business model, as a for-profit vs. a non-profit. So, let me explain those briefly.
The 4th episode of the Gate 15 Podcast is now available! There is a lot of information “out there” related to the COVID-19 pandemic – some of which is true and useful… Aside from initial reactions, the team looks ahead to what’s next as this pandemic continues and how do we start preparing to handle other incidents – from spring flooding and an upcoming hurricane season to potential hostile events – in a COVID world.
With multiple COVID-19 updates per day from myriad sources, scammers are predictably using every conceivable (and even inconceivable) lure to hide their cyber attacks in plain sight.
As coronavirus has shown, the impacts of a pandemic can wreak havoc worldwide, quickly and severely. At some point, things will start to get back to “normal,” and there will be a big push to catch up and make up for lost time. While it would be easy for many to get through this pandemic and reassure ourselves, “this happens every hundred years,” and to then try to resume “normal” routines and operations, focusing on the next requirement and not the past – that would be a huge mistake, and an even more huge missed opportunity.
By a Gate 15 Team Member I’m honored and grateful to work for Gate 15, a small veteran-owned business, that…
So much can change in a month. Last month we touched on COVID-19, and in this episode we dig more into questions about preparedness and the resulting cyber scams associated with it. Then we transition to other cyber issues, specifically Business Email Compromise and phishing.
03 February 2020 Our newest podcast is available now! Dave Pounder, Gate 15’s Director for Threat and Risk Analysis, and…
Our team at Gate 15 is looking forward to a project we’ve been wanted to develop for a few years,…
As 2019 turns into 2020, technologies and threats that impact daily operations and data security persist in blended and complex ways. The convergence of both physical and cyber domains increase the productivity and value of businesses and critical infrastructure at large, but introduce new and evolving risks that can harm assets and individuals when the line between IT and physical risks are no longer crystal clear.
By Omar Tisza At Gate 15, we tirelessly devote our time and resources to support the Homeland Security Mission through…
As enterprises and security minded organizations keep contending with the physical and cyber components of security, the merging of both physical and cyber realms necessitates a similar security approach to strengthen and maintain the foundations of our critical infrastructure.
By Brett Zupan Last year, I wrote a blog about the varied threats that higher education security professionals have to…
By Andy Jabbour In establishing Gate 15, one area I hoped to develop was the idea of service. As a…
By Mayya Saab National Preparedness Month is recognized each September to promote family and community disaster as well as emergency…
In this update on threats that are neither entirely comprised of physical or cyber parts, known as blended and complex threats, we explore their complexities and consequences as they become relevant to the security and resiliency of our critical infrastructure
A webinar for the RE-ISAC by Trend Micro’s Numaan Huq and Stephen Hilt, and a panel discussion including Numaan, Stephen and Gate 15’s Jennifer Walker.
We use the term blended and complex threats to account for threats that operate within and cross-over physical and cyber boundaries. This post includes examples of the terms above contextualized in recent incidents and vulnerabilities.
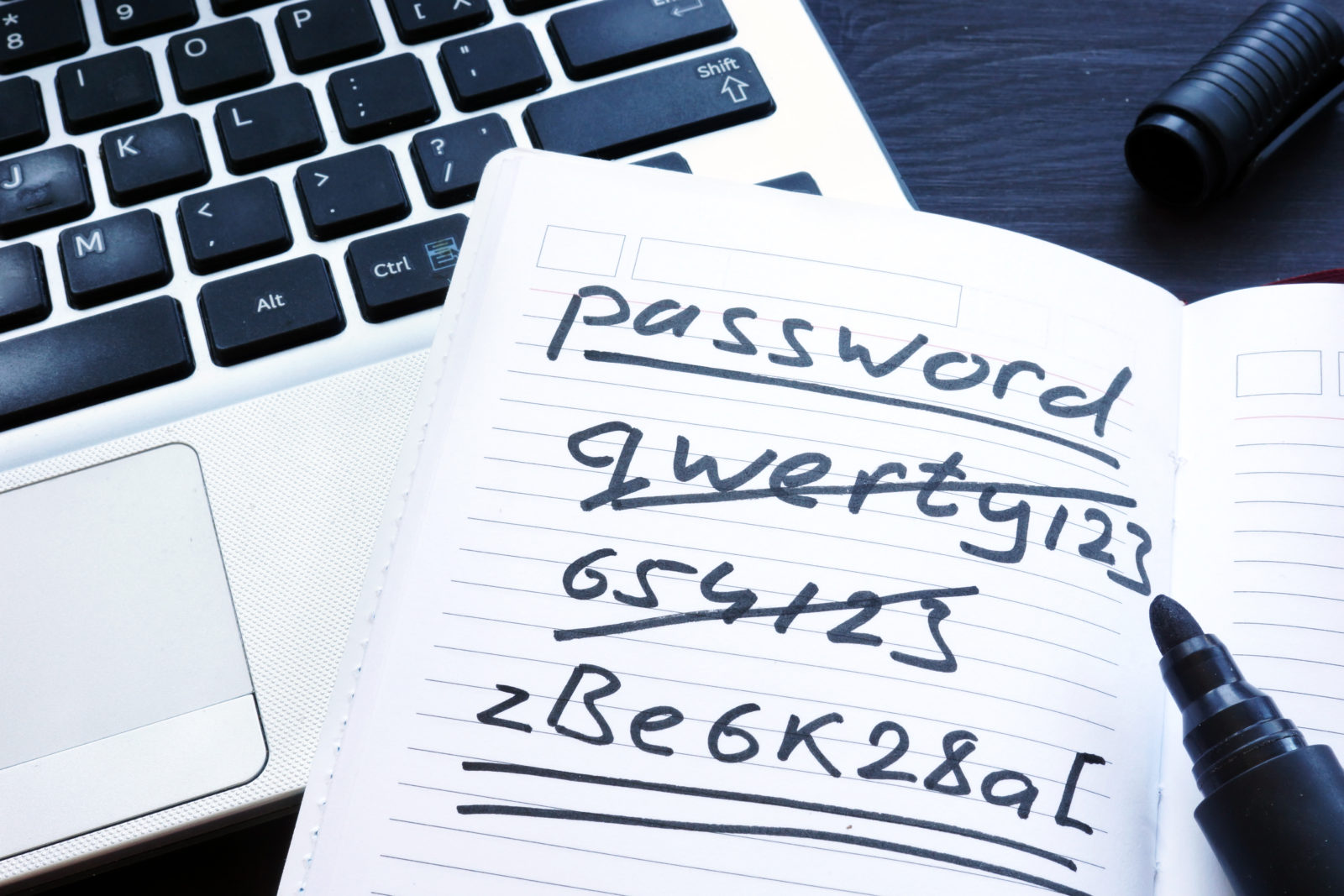
Three simple things that anyone can to do to maintain reasonable password security.
By Omar Tisza As cyber-adversaries become sophisticated in their attacks against critical infrastructure, we see the level of sophistication between…
By Mayya Saab This January, our team gathered for one of our too infrequent in-person all-hands huddles. Among the other…
By Omar Tisza In our quest to continue exploring salient examples of complex and blended threats, we have complied a…
I often get asked, “what is Gate 15” or “what does that mean?” A lot of folks assume it has…
by Andy Jabbour Too many cookies, another Detroit Lions loss, and a slew of predictions for next year… it…
By Omar Tisza Cyber threats are increasingly gaining the full attention of industry and–most recently–government as the Department of…
By Andy Jabbour Eleven months ago, I wrote: Following the House of Representatives, the US Senate needs to approve…
Over the course of this year, our team has shared a number of posts regarding blended and complex threats. As…