On 12 Oct 2021, Josh Meyer, @JoshMeyerDC, wrote an article titled, “The next big cyberthreat isn’t ransomware. It’s killware. And it’s…
In the latest edition of Nerd Out, Dave is joined by nerdette Bridget Johnson, and nerd Joe Levy to take…
This month, the National Council of ISACs (NCI) published a new paper, National Council of ISACs Statement of Ransomware, stating,…
Our team at Gate 15 appreciates the valuable alerts, guidance and products developed and shared by our government partners, at…
In this episode of The Gate 15 Interview, Andy Jabbour talks with Mark Arena, CEO, Intel 471. Mark on Twitter: @markarenaau. Mark on LinkedIn.…
In this episode of The Gate 15 Interview, Andy Jabbour talks with Amanda Mason, Vice President, Intelligence, Related Companies. “Our passion for urban…
After a a busy couple of weeks, the merry band of Nerdies gathered to discuss the latest news on the…
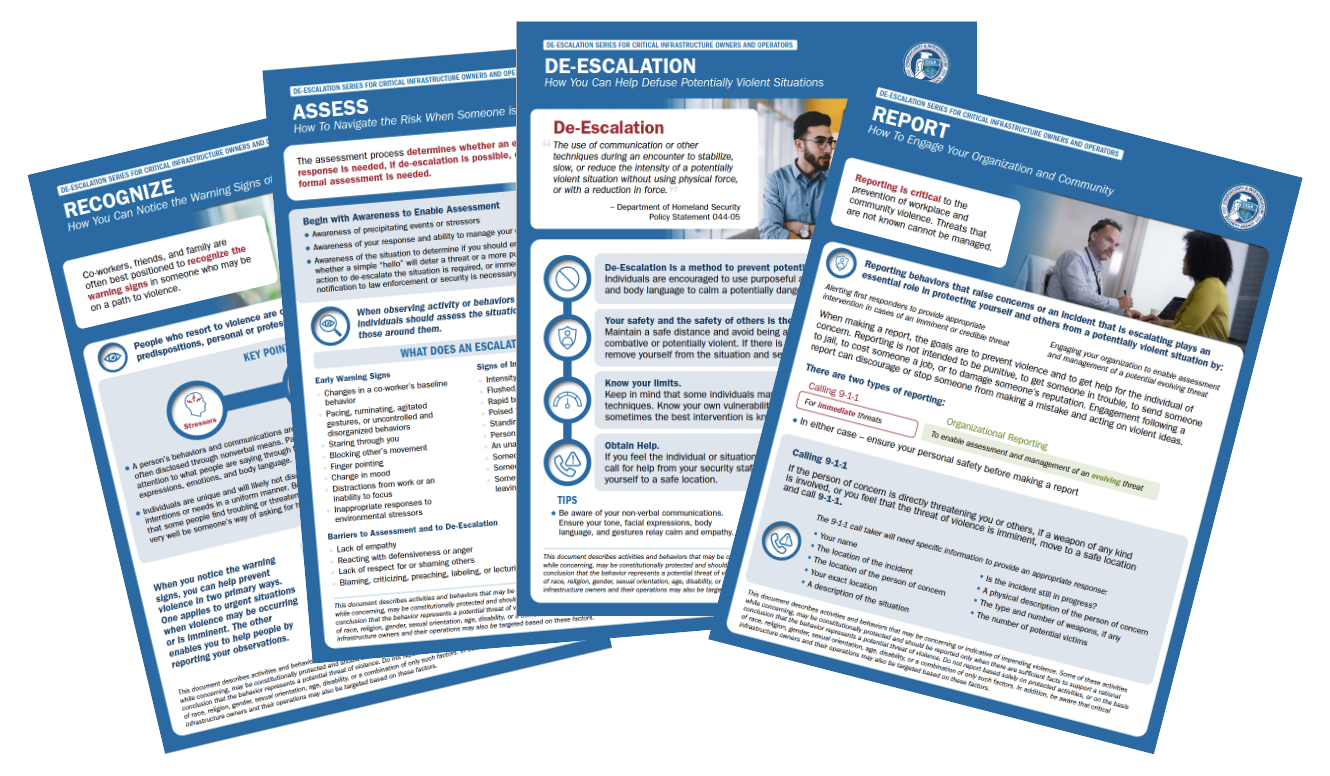
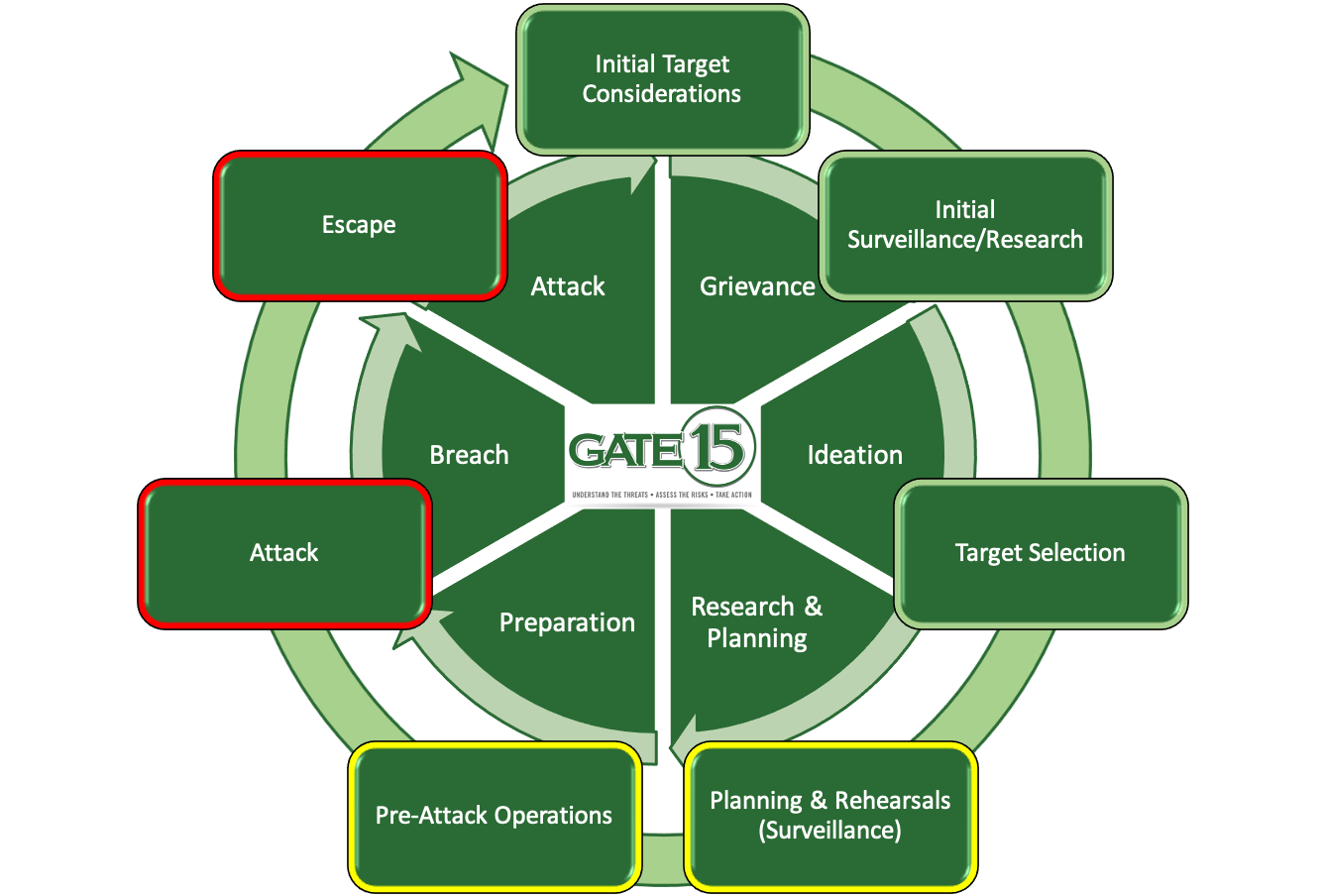
The Hostile Event Attack Cycle Identifies the Phases a Threat Actor Employs Prior to Perpetrating an Attack on Innocent Lives…
Please enjoy this month’s episode of The Gate 15 podcast on Anchor, Spotify, Apple, Google, as well as other locations accessible via the Anchor…
In this episode of The Gate 15 Interview, Andy Jabbour talks with Peter Ashwin, the principal and founder of Event Risk Management…
Please enjoy this month’s episode of The Gate 15 podcast on Anchor, Spotify, Apple, Google, as well as other locations accessible via the Anchor…
By Andy Jabbour This is a small update to a post shared a year ago, “The SUN also rises… (a…
Please enjoy this month’s episode of The Gate 15 podcast on Anchor, Spotify, Apple, Google, as well as other locations accessible via the Anchor…
Please enjoy this month’s episode of The Gate 15 podcast on Anchor, Spotify, Apple, Google, as well as other locations accessible via the Anchor…
Please enjoy this next episode of The Gate 15 Podcast on Anchor, Apple, Spotify, as well as other locations accessible…
The Risk Roundtable: EP 11 – Protests & Security Awareness Months (Preparedness! Insider Threats!! Cybersecurity!!!) Please enjoy this next episode…
the Gate 15 team discusses geopolitics and the impacts they have on organizations around the world. The team touches on security concerns around current issues including U.S.-China tensions and why TikTok is a topic of discussion and the idea that how nations and leaders see each other – as adversaries or competitors – is also an important consideration. Listen to Dave, Jorhena, Jen, and Andy then speak on the importance of partnerships and the need to build and engage in trusted relationships and information sharing. But they couldn’t completely escape the enduring threats of ransomware and COVID, and they weighed in on the continued impact it is having on sports leagues while hearing Andy’s hope for his favorite football team. Andy also shares his current earworm struggles and gets mocked for his choice of attire…
The people have spoken! The Gate 15 Pod has now become the Risk Roundtable. In this episode the gang is…
Illustrating how rapidly and dangerously this can play out in our world today, Sarah Coble reported, that the life of Jessica Hatch, a Houston business owner, was “threatened after cyber-criminals hacked into her company’s social media account and posted racist messages.
I get asked a lot of questions about Gate 15, like, “what does Gate 15 mean?” (see here – Gate 15: What’s in a Name?
– for that answer). I also get a lot of questions about two other areas. One of those is about the SUN, our free daily online paper. The other is about our business model, as a for-profit vs. a non-profit. So, let me explain those briefly.
So much can change in a month. Last month we touched on COVID-19, and in this episode we dig more into questions about preparedness and the resulting cyber scams associated with it. Then we transition to other cyber issues, specifically Business Email Compromise and phishing.
03 February 2020 Our newest podcast is available now! Dave Pounder, Gate 15’s Director for Threat and Risk Analysis, and…
Our team at Gate 15 is looking forward to a project we’ve been wanted to develop for a few years,…
By Omar Tisza As cyber-adversaries become sophisticated in their attacks against critical infrastructure, we see the level of sophistication between…
By Mayya Saab This January, our team gathered for one of our too infrequent in-person all-hands huddles. Among the other…
By Omar Tisza In our quest to continue exploring salient examples of complex and blended threats, we have complied a…
by Andy Jabbour Too many cookies, another Detroit Lions loss, and a slew of predictions for next year… it…
By Omar Tisza Cyber threats are increasingly gaining the full attention of industry and–most recently–government as the Department of…
Over the course of this year, our team has shared a number of posts regarding blended and complex threats. As…