By Andy Jabbour In Brief: Security, preparedness, and resilience – whether focused on terrorism, health risks, natural hazards, cybersecurity,…
By Andy Jabbour Following the House of Representatives, the US Senate needs to approve the re-designation of DHS’s National…
By Andy Jabbour November is National Critical Infrastructure Security and Resilience Month (NCISRM), and I’m very excited to work with…
By Jennifer Kazy If you are a Doctor Who fan, you likely recognize the title used for this post in…
By Kristi Horton The “Most Wonderful Time of the Year” is coming – and much sooner than many of us…
By Andy Jabbour Concluding the series we’ve been writing with our friends at SurfWatch Labs on applying the Preparedness Cycle to Cyber…
Today’s post wraps up the series we’ve been writing with our friends at SurfWatch Labs on applying the Preparedness Cycle to Cyber…
Today’s post concludes our mini-series within a series, as we complete the posts addressing he planning and conduct of exercises…
Today’s post continues the fifth part of our ongoing series on applying the Preparedness Cycle to Cyber Risk Management. This…
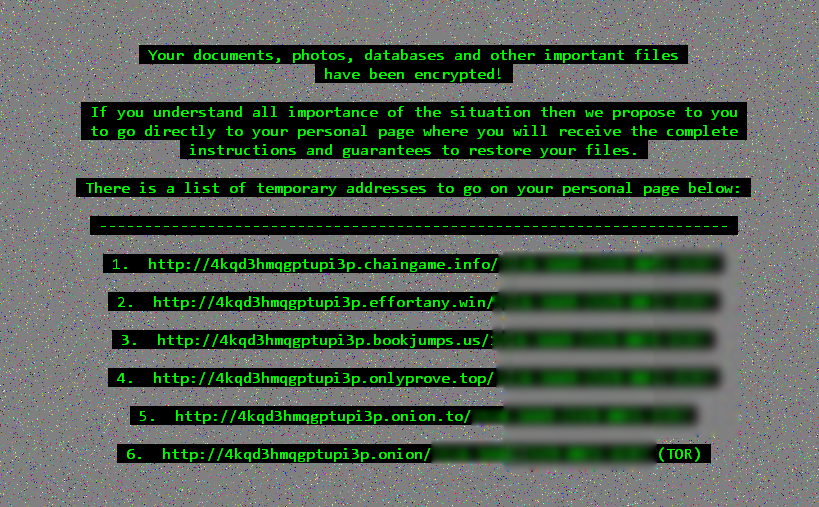
In our 16 May 2017 blog post, we addressed the WannaCry outbreak and how the cyber-incident highlighted the ineffectiveness of…
Today’s post begins the fifth part of our ongoing series on applying the Preparedness Cycle to Cyber Risk Management. This…
On 27 July, Gate 15’s Kristi Horton and SurfWatch Labs’ Adam Meyer addressed: Recent extortion and ransomware attacks against entertainment…
This is the fourth in a short series we’re writing for our friends at SurfWatch Labs on applying the Preparedness…
This is the third in a short series we’re writing for our friends at SurfWatch Labs on applying the Preparedness…
This is the second in a short series we’re writing for our friends at SurfWatch Labs on applying the Preparedness…
About a week ago, as we were coming out of the initial concerns relating to the WannaCry ransomware outbreak, I…
Business Email Compromise (BEC) is a more specific form of Email Account Compromise (EAC). Email accounts can be compromised by…
Vocabulary.com defines extortion as “forcing someone into giving you something through threats.” Most commonly the extortioner desires money but it…
This is the first in a short series we’re writing for our friends at SurfWatch Labs on applying the Preparedness…
Recently, two Gate 15 team members – Kristi Horton, Senior Risk Analyst in Cybersecurity, and Chip Wickenden, Director of Strategic…
The purpose of the Gate 15 Threat and Risk Analysis Cell (TRAC) is to be aware of threat patterns and its analysis…
In this reporting period, the the Gate 15 Threat and Risk Analysis Cell (TRAC) honed in on four notable areas of concern in Wednesday’s…
This week, our team looked at a variety of issues and concerns, including Bird Flu’s global footprint and, taking a…