The 4th episode of the Gate 15 Podcast is now available! There is a lot of information “out there” related to the COVID-19 pandemic – some of which is true and useful… Aside from initial reactions, the team looks ahead to what’s next as this pandemic continues and how do we start preparing to handle other incidents – from spring flooding and an upcoming hurricane season to potential hostile events – in a COVID world.
With multiple COVID-19 updates per day from myriad sources, scammers are predictably using every conceivable (and even inconceivable) lure to hide their cyber attacks in plain sight.
So much can change in a month. Last month we touched on COVID-19, and in this episode we dig more into questions about preparedness and the resulting cyber scams associated with it. Then we transition to other cyber issues, specifically Business Email Compromise and phishing.
03 February 2020 Our newest podcast is available now! Dave Pounder, Gate 15’s Director for Threat and Risk Analysis, and…
Our team at Gate 15 is looking forward to a project we’ve been wanted to develop for a few years,…
As 2019 turns into 2020, technologies and threats that impact daily operations and data security persist in blended and complex ways. The convergence of both physical and cyber domains increase the productivity and value of businesses and critical infrastructure at large, but introduce new and evolving risks that can harm assets and individuals when the line between IT and physical risks are no longer crystal clear.
As enterprises and security minded organizations keep contending with the physical and cyber components of security, the merging of both physical and cyber realms necessitates a similar security approach to strengthen and maintain the foundations of our critical infrastructure.
By Brett Zupan Last year, I wrote a blog about the varied threats that higher education security professionals have to…
In this update on threats that are neither entirely comprised of physical or cyber parts, known as blended and complex threats, we explore their complexities and consequences as they become relevant to the security and resiliency of our critical infrastructure
A webinar for the RE-ISAC by Trend Micro’s Numaan Huq and Stephen Hilt, and a panel discussion including Numaan, Stephen and Gate 15’s Jennifer Walker.
Three simple things that anyone can to do to maintain reasonable password security.
By Omar Tisza As cyber-adversaries become sophisticated in their attacks against critical infrastructure, we see the level of sophistication between…
By Mayya Saab This January, our team gathered for one of our too infrequent in-person all-hands huddles. Among the other…
By Omar Tisza In our quest to continue exploring salient examples of complex and blended threats, we have complied a…
by Andy Jabbour Too many cookies, another Detroit Lions loss, and a slew of predictions for next year… it…
By Omar Tisza Cyber threats are increasingly gaining the full attention of industry and–most recently–government as the Department of…
Over the course of this year, our team has shared a number of posts regarding blended and complex threats. As…
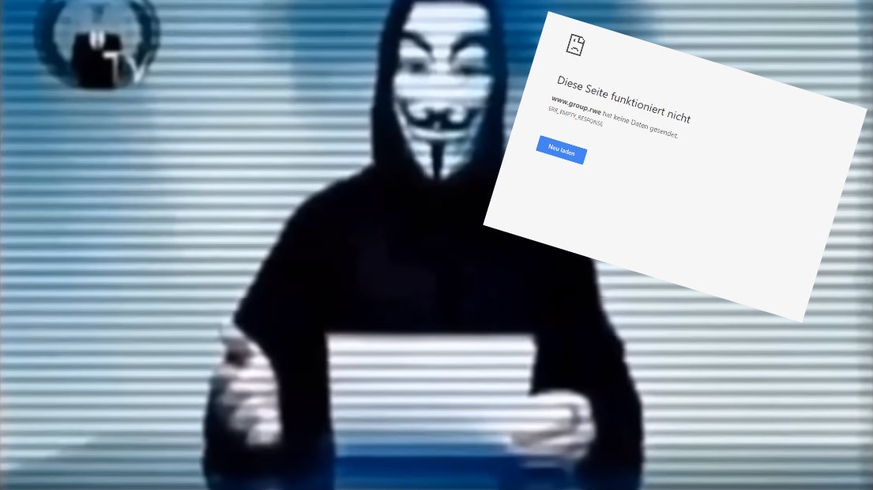
“If you don’t immediately stop the clearing of the Hambach Forest, we will attack your servers and bring down your…
by Andy Jabbour Seemingly every day a new data breach is reported, a new cybercrime effort is launched, fraud and extortion…
“Cyberattacks have always been, well, cyber. Their immediate effects were on our data, our digital information, and our devices…until they…
A new report from the Cyber Threat Alliance (CTA) highlights one type of blended threat that organizations should be aware…
Sean Lyngaas, @snlyngaas, writing in CyberScoop last week, wrote, “When it comes to protecting faith-based organizations from hackers, divine intervention will…
In this blog, we’ve written a few times about the idea of “Blended Threats,” and some of the ways the…
By Brett Zupan There is a tremendous amount of information that analysts, security and risk leaders, executives, and others…
In a recent post introducing the preparedness efforts that the National Health Information Sharing and Analysis Center (NH-ISAC) is taking to…
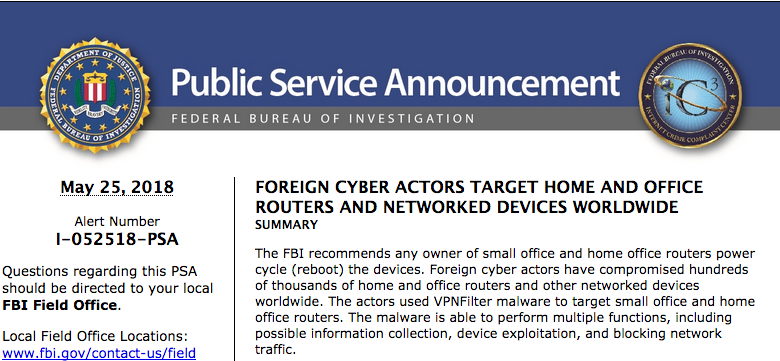
It is rare that the US Government asks everyone to do something, and it can be challenging to get that…
By Brett Zupan and Andy Jabbour Across critical infrastructure, organizations must continually reassess their risks based on an ever-changing…
By Andy Jabbour This is an update to the original post, “Terminology for $500. What Are Blended Attacks?” 26 May…
By Andy Jabbour There is a tremendous amount of information that analysts, security and risk leaders, executives, and others…