Researchers at cybersecurity firm Trellix (@Trellix, @TrellixLabs) found eight vulnerabilities in the LNL-4420 panel, made by HID and distributed by Carrier, which allowed them to take full control of the device. As reported by Lorenzo Franceschi-Bicchierai, @lorenzofb, in Vice/@VICE, this would have allowed them to remotely lock and unlock the doors controlled by the device, allowing them to steal valuable hardware or access sensitive computers inside whatever building that was protected by the access control system.
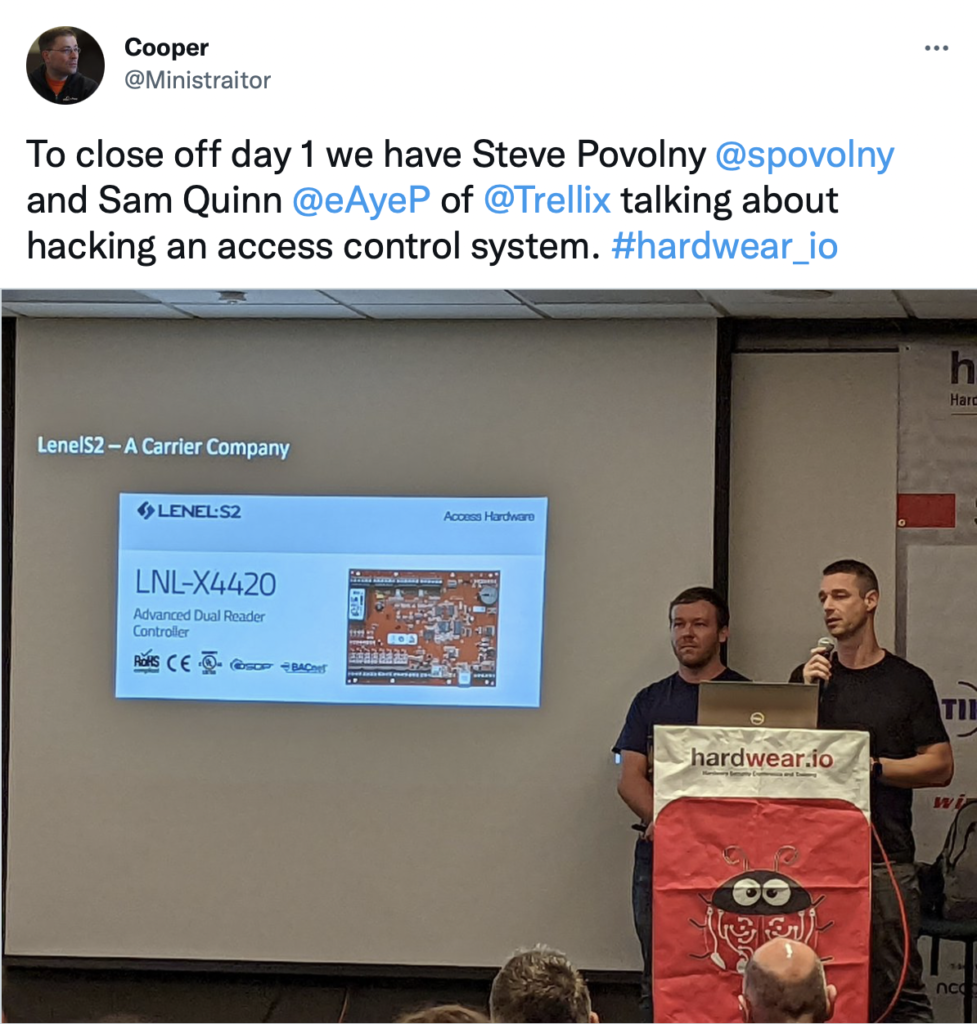
“With that level of access, we could unlock the doors, bypass all sorts of monitoring and really control the device in like a god mode state,” Sam Quinn/@eAyeP, a senior researcher at Trellix, told Motherboard in a phone call.
A similar attack has reportedly happened in the real world when a volunteer group of technologists and hackers known as the Ukraine IT Army hacked into the network of RuTube, Russia’s largest streaming service and YouTube competitor. As Lorenzo reported earlier this year, the hackers claimed to not only have taken down RuTube’s site for three days, but also have hacked into the system that controlled access to the company’s server rooms, locking people inside.

Our team at Gate 15 has been very grateful to work closely with the Commercial Facilities Sector and the Real Estate ISAC (RE-ISAC)/@RealEstateISAC for many years. RE-ISAC works with members, partners and other information sharing groups around the country and internationally to prevent, protect against, mitigate, respond to, and recover from all-hazards, including cyber threats and vulnerabilities, as well as physical security, health threats, and natural hazards. If you or your organization identify issues or concerns affecting facilities, please contact our team to help educate and inform appropriate stakeholders and to assist in threat reduction and vulnerability management.
Understand the Threats.
Assess the Risks.
Take Action.
Understand the threats! Subscribe to our free daily paper and subscribe to our podcasts!
Take action! Our team specializes in intelligence and analysis, preparedness activities to include the development of plans, training, and exercises, and we can help you build the relationships and capabilities you need for effective information sharing operations to support your ability to prevent, protect against, mitigate, respond to, and recover from the threats and hazards that pose the greatest risk to your organization in our complex, all-hazards environment.
